
Newsletter Subscribe
Enter your email address below and subscribe to our newsletter

You’re sipping your morning coffee, minding your own business, when you get an email. It says a massive corporation—one you bought a single pair of socks from in 2014—has experienced a “data security incident.” Suddenly, your personal information is floating around the internet like confetti at a parade, and you’re left wondering if you should just move into a cave and pay for everything with shiny rocks.
If this scenario makes your blood pressure spike, take a deep breath. You are absolutely not alone. In 2025 alone, there were a staggering 166 million data breaches in the US, exposing billions of records.
When you hear that a database containing 2.7 billion Social Security numbers has been breached, it’s completely normal to feel a wave of sheer panic. But panic is exactly what scammers are hoping for. The truth is, managing a data breach is a lot like dealing with a flat tire. It’s highly annoying, it ruins your afternoon, but it is completely fixable if you know exactly which tools to use.
We’re going to walk through this together. No confusing tech jargon, no corporate double-speak, and definitely no tech-shaming. Just a clear, step-by-step roadmap to locking down your digital life and keeping your hard-earned money exactly where it belongs.
The hardest part of a data breach is the waiting game. You know something happened, but you don’t know if your specific data was in the digital filing cabinet that got raided. Thankfully, you don’t have to wait for a sluggish corporate apology letter in the mail to find out.
There is a highly trusted, free website called “Have I Been Pwned.” I know, it sounds like a phrase a teenager made up while playing video games—because it is. But despite the silly name, it is a secure tool built by top cybersecurity experts and recommended by governments worldwide.
You simply type your email address into the search bar, and the site instantly checks it against a massive database of known breaches. It won’t ask for your password or your Social Security number. If your screen turns green, you’re in the clear. If it turns red, it will tell you exactly which companies lost your data so you know where to start cleaning up.
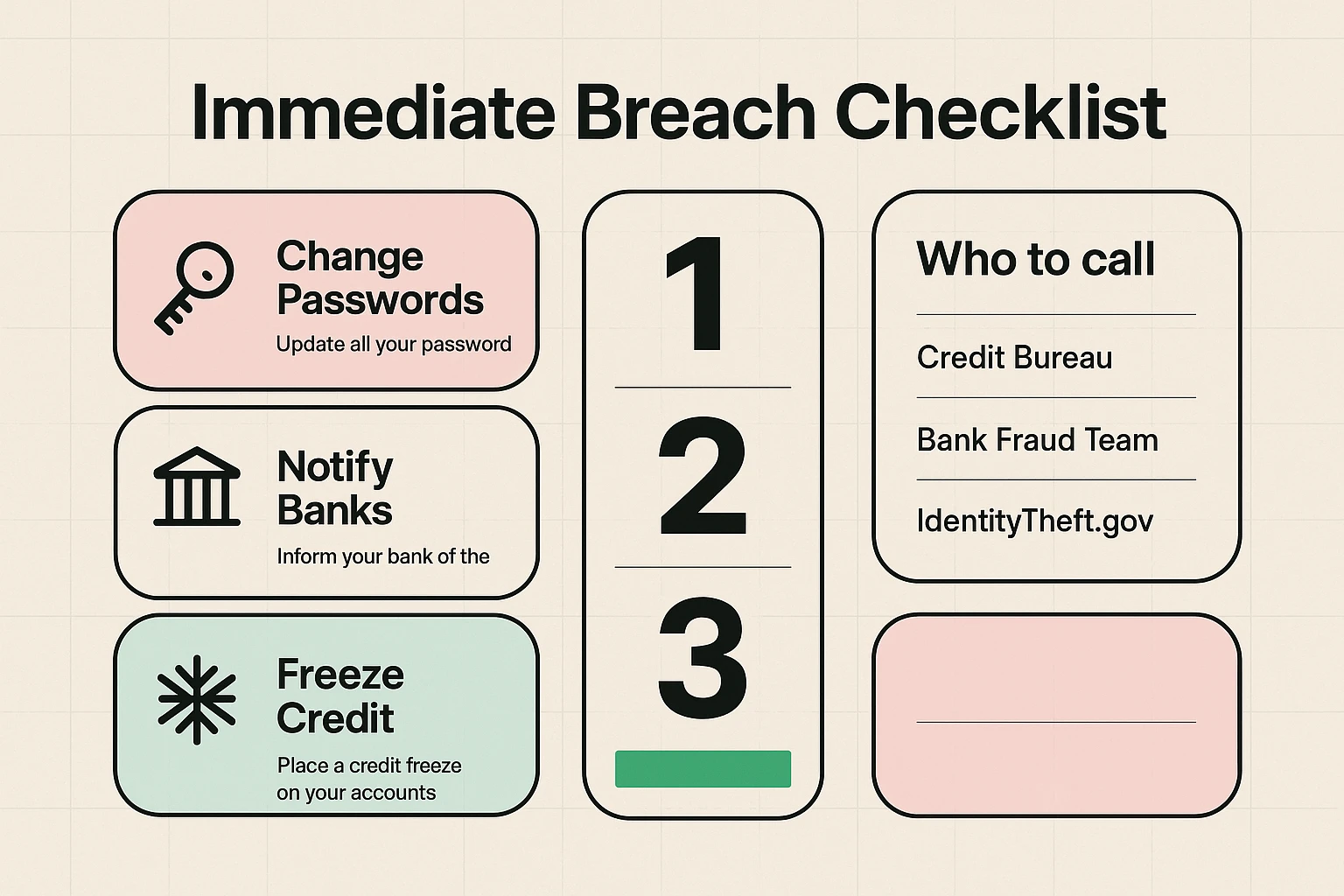
So, you’ve confirmed your data was part of a breach. Now it’s time to spring into action. Think of these steps as the digital equivalent of changing the locks on your front door.
First, change your passwords for the affected accounts immediately. And please, if your password is still “Fluffy2009” or “Password123,” it’s time for an upgrade. Research shows that credential theft drives 22% of all data breaches, meaning hackers literally just log in using stolen passwords. A good password manager can help you create and remember complex passwords without needing a photographic memory.
Next, initiate a credit freeze. A credit freeze is like putting a titanium deadbolt on your credit report. It stops anyone—including you—from opening new credit cards or loans in your name. It is completely free, does not hurt your credit score, and you can thaw it out temporarily anytime you actually need to buy a car or open a new account. You’ll need to contact all three major bureaus (Equifax, Experian, and TransUnion) separately to set this up.
Finally, call your bank or credit card company if financial information was exposed. Don’t use the phone number in the scary email you received (that could be a trick). Flip your credit card over and call the number printed right there on the back of the plastic.
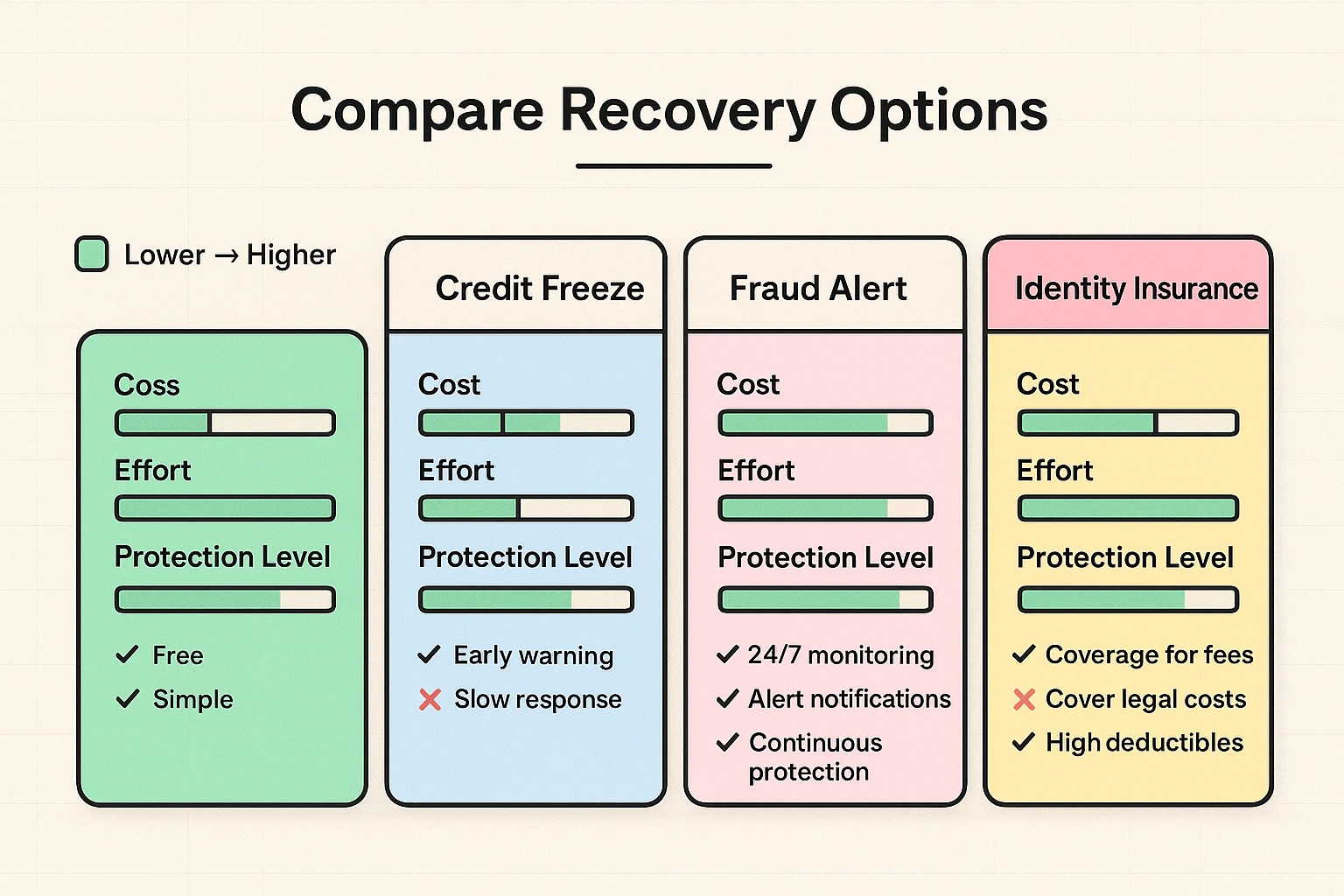
If your identity has actually been stolen—meaning someone is actively using your information—you have a few different paths to take. You don’t have to hire a high-priced lawyer right out of the gate, but you do need to decide how much hands-on help you want.
The DIY route involves using IdentityTheft.gov, a fantastic official resource from the Federal Trade Commission (FTC). They will ask you a few questions and automatically generate a personalized recovery plan, including pre-written letters to send to debt collectors. It’s totally free, but you’ll have to do the legwork of mailing letters and making phone calls yourself.
Alternatively, you might opt for a paid Identity Theft Protection service (like LifeLock or Aura). These services cost a monthly fee, but they actively monitor your credit, alert you to suspicious activity, and often provide insurance to cover stolen funds. Just remember, no service can prevent a breach from happening; they just help you clean up the mess faster when it does.
Here is a cruel irony: when scammers hear about a massive data breach on the news, they don’t just use the stolen data. They use the news of the breach itself to trick you. Since human error is responsible for 74% to 95% of all cybersecurity incidents, scammers know that tricking a stressed-out human is much easier than hacking a computer.
You might get a frantic phone call from someone claiming to be from “The Fraud Department” or “Medicare,” stating that your account has been breached and you need to verify your Social Security number to secure it. Hang up the phone. Legitimate organizations will never call you out of the blue and ask for your full Social Security number or your passwords.
If you want a handy cheat sheet to keep near your computer, grab our online scamming methods pdf free download to help you spot these fakes from a mile away. Remember, when in doubt, hang up, look up the official phone number yourself, and call them directly.
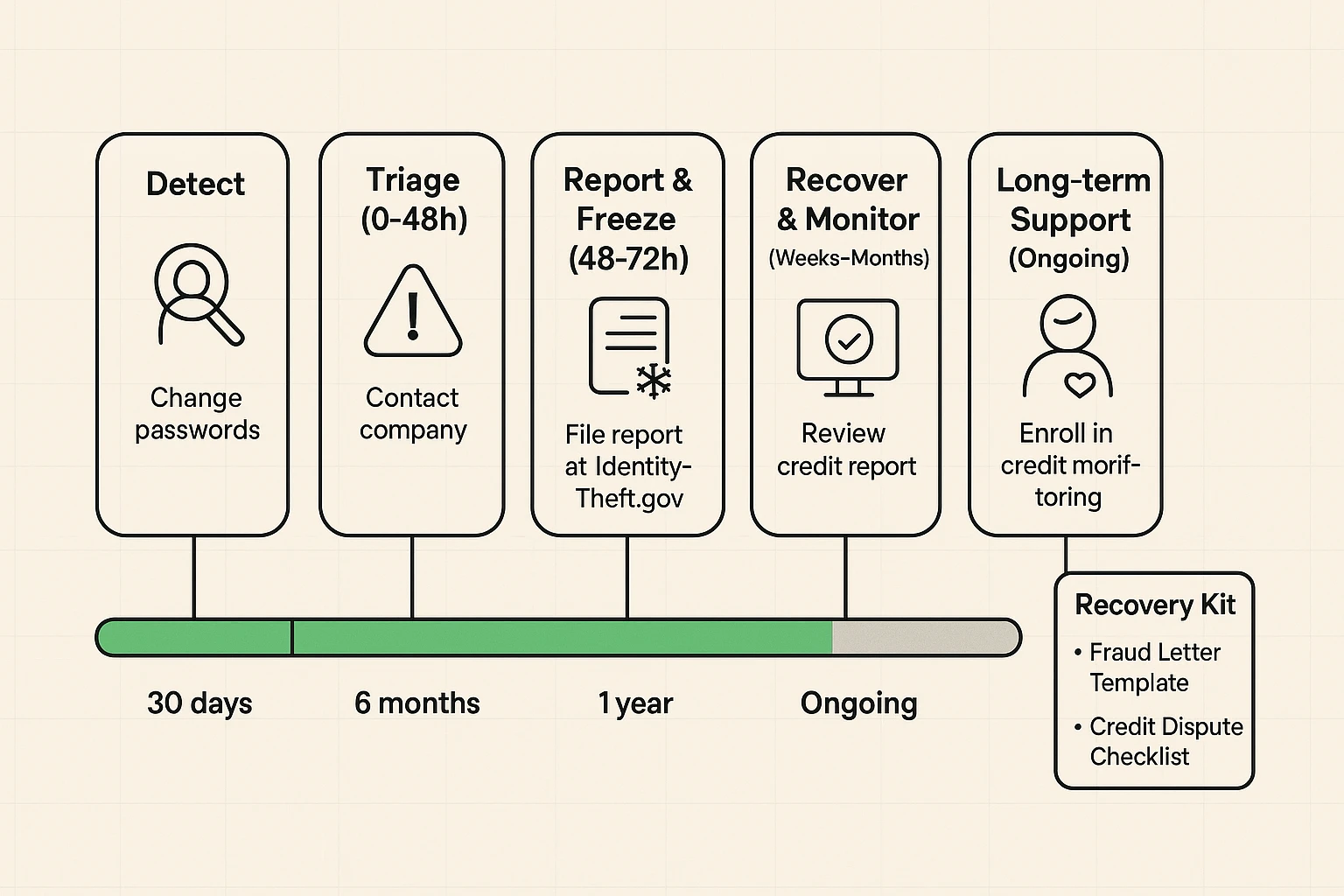
Recovering from a data breach isn’t a one-and-done chore like taking out the trash. It’s more like tending to a garden; you have to keep an eye out for weeds. Older adults experience $3.4 billion in identity theft losses annually, representing 41% of all financial losses despite making up only 24% of the claims. That means when seniors are hit, they are hit incredibly hard.
Make it a habit to review your bank and credit card statements every single month. Look for tiny, bizarre charges. Scammers will often test a stolen card by charging $1.50 for a digital download or a cup of coffee halfway across the country. If the small charge goes unnoticed, they come back the next day and buy a flat-screen TV.
You should also check your credit report for free once a year at AnnualCreditReport.com. If you see a loan for a jet ski and you definitely don’t own a jet ski, you know you have a problem.
Not at all. A credit freeze has absolutely zero impact on your credit score. It just stops creditors from pulling your report to open a new account. You can still use your existing credit cards just like normal.
Maybe not. Before you open your wallet, check with your homeowner’s or renter’s insurance policy. Many of them include basic identity theft recovery assistance at no extra cost. Also, check if the company that breached your data is offering free credit monitoring. They often offer a year or two for free as an apology.
I hate to burst your bubble, but probably not. When a huge company gets sued for losing data, the lawyers take a massive cut. By the time the settlement trickles down to the millions of affected users, your payout might just be enough to buy a fancy cup of coffee. Claim the money if it’s offered, but don’t plan your retirement around it.
Data breaches are an unfortunate reality of modern life, much like junk mail and telemarketers calling right as you sit down for dinner. You can’t control what massive tech companies do with their servers, but you have complete control over how you respond.
By taking a few simple precautions—like freezing your credit, updating those tired old passwords, and keeping a watchful eye on your statements—you transform yourself from an easy target into a digital fortress.
Technology is supposed to make our lives easier, not keep us up at night. If you found this guide helpful and want more plain-English, hype-free advice delivered straight to your inbox, make sure to sign up for the Senior Tech Cafe newsletter. We’ll keep translating the tech world for you, one simple step at a time.