
Newsletter Subscribe
Enter your email address below and subscribe to our newsletter

You’re just sitting down to a hot, lovingly prepared dinner. The phone rings. You leap up, sprint across the room with the agility of an Olympic hurdler, and grab the receiver. You expect to hear the sweet voice of your grandchild. Instead, a robotic voice named “Kevin” informs you that the extended warranty on your 2006 Honda Civic—a car you never even owned—is about to expire.
You shout, “I’m on the Do Not Call list!” at the dial tone, feeling a mix of righteous indignation and complete helplessness. It’s a frustrating ritual we all know too well. Adding your name to the National Do Not Call registry was supposed to be the magic shield that protected our peace and quiet. Yet, our phones continue to light up like pinball machines with scam calls and relentless telemarketers.
If this sounds familiar, you aren’t doing anything wrong. The truth is, the nature of spam calls has completely changed, but our defenses haven’t. Today, we are going to pull back the curtain on how these callers actually get your number, why the old rules no longer apply, and how you can finally reclaim your phone’s ringtone.
Let’s be honest, putting your number on the Do Not Call registry to stop scammers is a bit like putting up a “No Burglars Allowed” sign on your front lawn. Legitimate, law-abiding businesses will absolutely respect it. They don’t want to face massive government fines for bothering you during Jeopardy.
But the scammer operating a massive robocall sweatshop from a basement thousands of miles away? He doesn’t care about our laws. In fact, many malicious actors view the Do Not Call list as a highly convenient directory of active, working phone numbers.
So, if the list isn’t stopping the bad guys, how are they finding your number in the first place? The answer involves a massive, invisible industry that trades in your personal information every single day.
If you’ve ever wondered how these callers got your private cell number, blame the shadowy world of data brokers. Think of data brokers as the ultimate digital gossips. They legally collect tiny bits of your public information from all over the internet, package it into a neat little file, and sell it to the highest bidder.
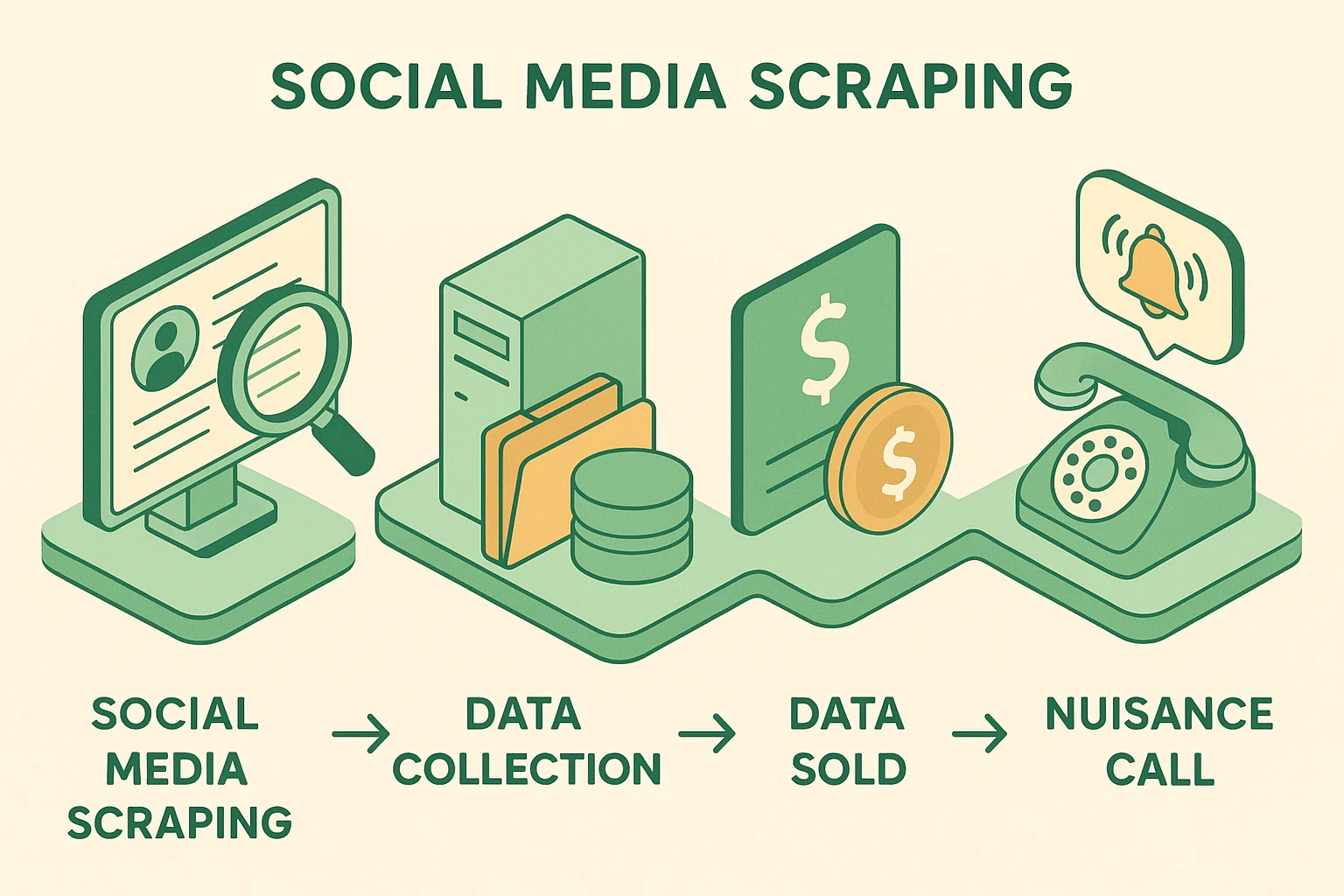
How do they get this info? Maybe you signed up for a grocery store loyalty program to save 40 cents on a jar of mayonnaise. Or perhaps your phone number was listed on a public club directory or social media page. Specialized computer programs, affectionately known as “scrapers,” harvest this public information faster than you can blink.
Three months later, the scrapers sell your data to a broker. The broker sells it to a marketing company, and suddenly, Kevin is calling you about that Honda Civic warranty. To stop the calls, we have to stop the flow of data at the source.

We need to stop playing the worst game of Whack-A-Mole ever invented. Blocking individual numbers on your phone is completely useless today. Scammers use something called “VOIP Spoofing,” a fancy tech term meaning they use internet software to fake their caller ID. Every time they call, it looks like a brand-new, local number.
To cut off the scammers, you can actually request to be removed from the major data broker websites like Spokeo, Whitepages, and Acxiom. It takes a little patience, but the law is on your side.
Most of these websites have a small link hidden at the very bottom of their homepage that says “Do Not Sell My Personal Information” or simply “Opt-Out.” Click that link, follow their specific steps, and you can snatch your personal phone number back from their digital clutches.
For mobile phones, your absolute best friend is a built-in setting called “Silence Unknown Callers.” Both iPhones and Androids have a version of this feature. Once activated, if a number isn’t already saved in your personal contact list, the phone won’t even ring. The call is quietly sent straight to voicemail.
This setting is an absolute lifesaver for your peace of mind. It is also incredibly effective for stopping a wangiri fraud attack—those sneaky “one-ring” scams designed to trick you into calling back a highly expensive, international premium rate number. If your phone never rings, you can’t fall for the trap.
For traditional landlines and VOIP home phones, contact your service provider and ask them to activate “Anonymous Call Rejection.” This simple feature acts like a digital bouncer, turning away anyone trying to hide their identity.
You might think reporting scammers to authorities like the FTC just sends your complaint into a giant bureaucratic black hole. However, regulators actually use these reports to identify massive scam networks.
They use your complaints to trace patterns and shut down the shady telecom companies providing the scammers with phone lines. It’s less about getting immediate personal revenge and more about contributing to a global neighborhood watch that protects everyone.
Thankfully, the cavalry is slowly arriving. Telecom companies are currently rolling out a government-mandated technology called STIR/SHAKEN. Despite sounding exactly like the instructions for James Bond’s famous martini, it’s actually a framework designed to digitally verify caller IDs.
Eventually, this technology will make it incredibly difficult for scammers to hide behind fake, local-looking numbers. When your phone company can’t verify who is calling, your screen will flag the call as “Scam Likely,” allowing you to ignore it with confidence. Until then, remember that any anonymous caller is essentially a red flag wrapped in a digital mystery.
Not at all. It works perfectly for keeping legitimate, law-abiding businesses from pestering you during your favorite TV shows. It’s just not designed to stop the criminals who operate entirely outside the law.
Scammers use advanced computer software to generate thousands of fake phone numbers every single minute. Blocking one individual number they used today is like trying to empty the ocean with a teaspoon. They’ll just call back tomorrow using a different fake number.
Yes, paid privacy services like DeleteMe or Incogni act as digital bodyguards, hunting down your data and submitting removal requests on your behalf. However, if you have the time and patience, you can do this yourself for free by visiting the data brokers’ websites directly.
Taking back control of your phone doesn’t require a degree in computer science. By understanding how your data flows and utilizing built-in tools like “Silence Unknown Callers,” you can finally enjoy dinner in peace. The robots can keep calling, but you don’t have to answer.