
Newsletter Subscribe
Enter your email address below and subscribe to our newsletter

Imagine you’re sitting down to watch your favorite evening quiz show, armed with a cup of tea and the smug satisfaction that you know the capital of Peru. Suddenly, the phone rings. It’s your grandson, Timmy. He sounds frantic. He says he’s in a Canadian jail because of a massive misunderstanding involving a rental car and a flock of aggressive geese, and he needs $2,000 in gift cards. Right now.
In the good old days, you’d know it wasn’t Timmy because the scammer usually sounded like a 40-year-old chain smoker reading from a script. Today, thanks to Artificial Intelligence, the voice on the phone sounds exactly like Timmy. His pitch, his tone, even his signature nervous chuckle—it’s all there.
It’s enough to send any loving grandparent into a state of sheer panic. But before you go clearing out your savings to bail “Timmy” out of goose-jail, let’s take a breath. The “Grandparent Scam” has gotten a high-tech facelift, but it still relies on one old-fashioned trick: getting you to act before you can think. Today, we’re going to turn you into your family’s Chief Security Officer so you can outsmart the scammers, even when your real grandkids won’t answer their phones.
You might be wondering, “How on earth did they get a recording of my granddaughter to sound so realistic?” They didn’t need to bug her phone like a villain in a 1970s spy movie.
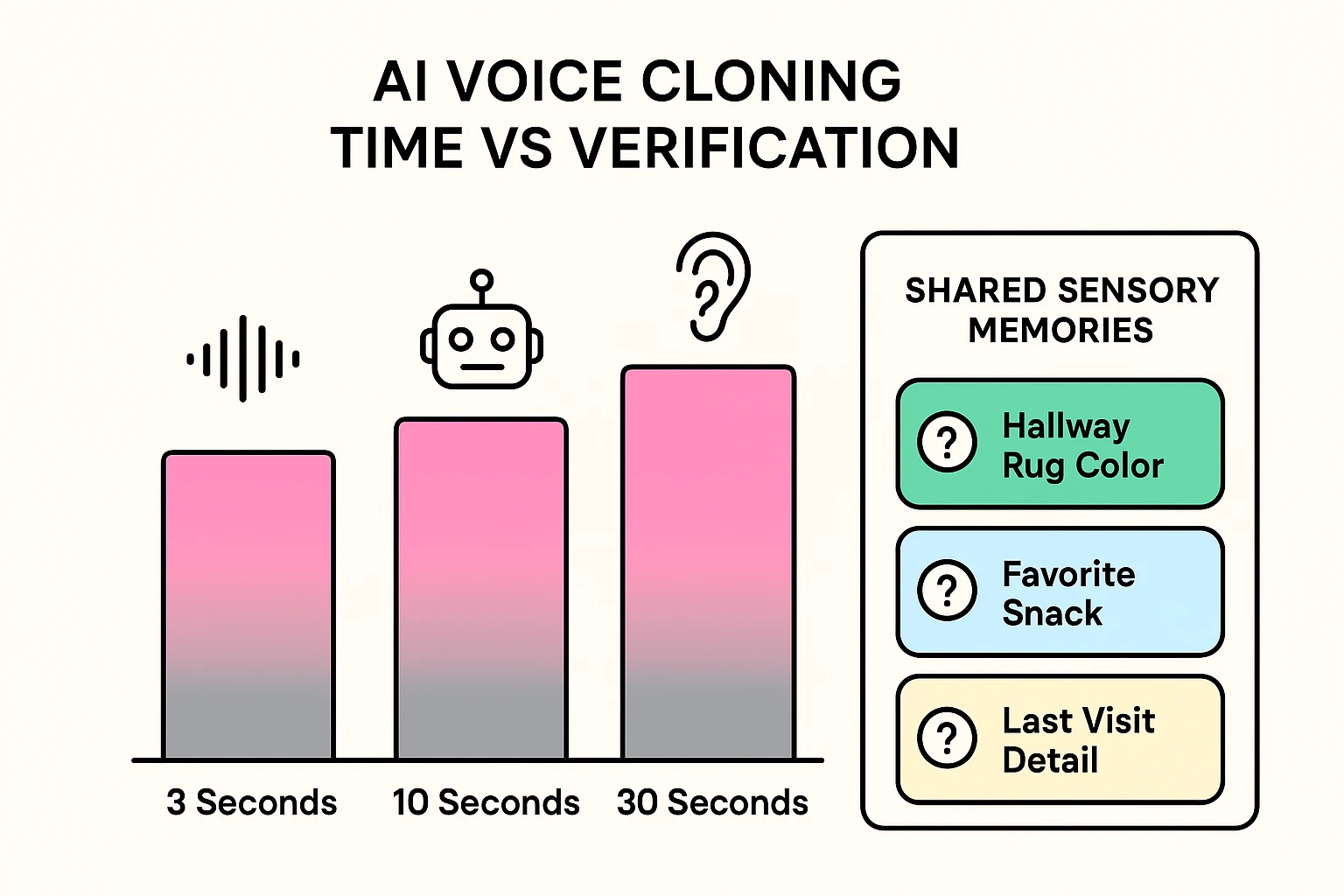
Scammers today just need about three seconds of audio from a public TikTok video or an Instagram post. That’s roughly the time it takes to say, “Hey guys, check out my new haircut.” With that tiny digital snippet, AI software can clone a voice and make it say literally anything.
It’s a terrifying parlor trick, to be sure. But knowing how the trick works is the first step to ruining the magician’s act. Once you accept that your ears can no longer be trusted, you can start using your brain to verify the facts.
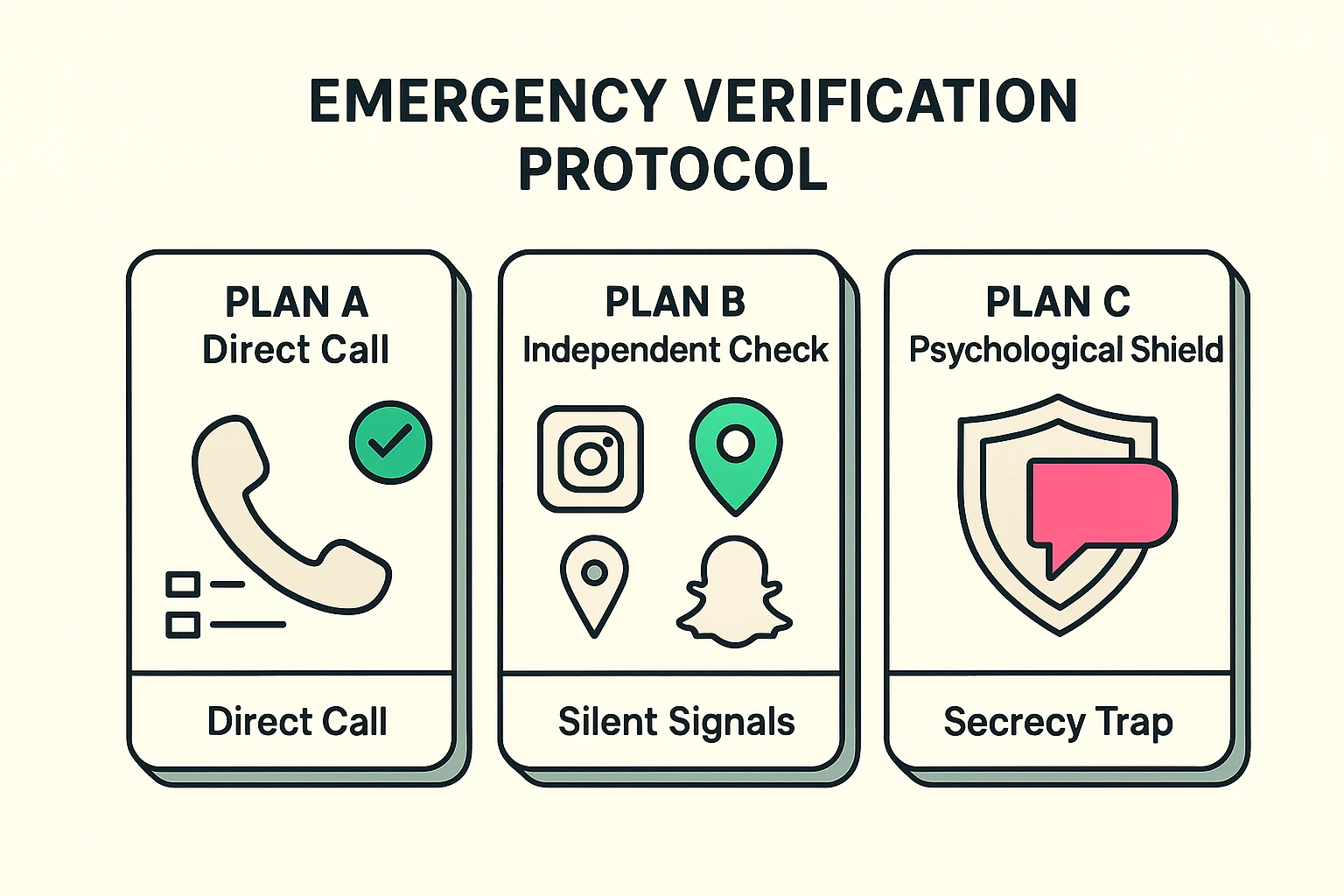
The standard advice you’ll hear from government agencies is simple: hang up and call them right back on their real number. It’s excellent advice!
If you call Timmy’s actual phone number and he answers from his college dorm while eating instant ramen, the mystery is solved. You can tell him you love him, hang up, and get back to your quiz show.
But what if he doesn’t answer? This is what we call the “Unreachable Moment.” It’s that terrifying blackout period where the phone goes straight to voicemail, panic sets in, and all logic packs its bags and moves to Florida.
This is the exact gap where scammers make their money. They are counting on the fact that your grandchild is probably in class, at a movie, or sleeping, and therefore unreachable. When Plan A fails, it’s time for Plan B: The Independent Verification.
First, check the “Silent Signal.” Ask another family member to check the supposedly jailed grandchild’s digital footprint. If Timmy is supposedly languishing in a cell, but his Venmo account shows he just bought a $7 latte three minutes ago, he’s probably not incarcerated.
Second, utilize the “Family Hub.” Every family has that one central command person—usually a mom, an aunt, or a sister—who knows everyone’s exact coordinates at all times. Call them immediately to see if they know where the grandchild is.
Finally, if the caller texts you a link claiming it’s for “emergency bail funds,” absolutely do not click it. Modern technology provides ways to fight back; for instance, you can use a bitdefender scam detector to safely analyze suspicious texts or links without putting your device at risk.
Scammers know you might try to verify their story. So, they deploy their ultimate psychological weapon to stop you in your tracks: The Secrecy Trap.
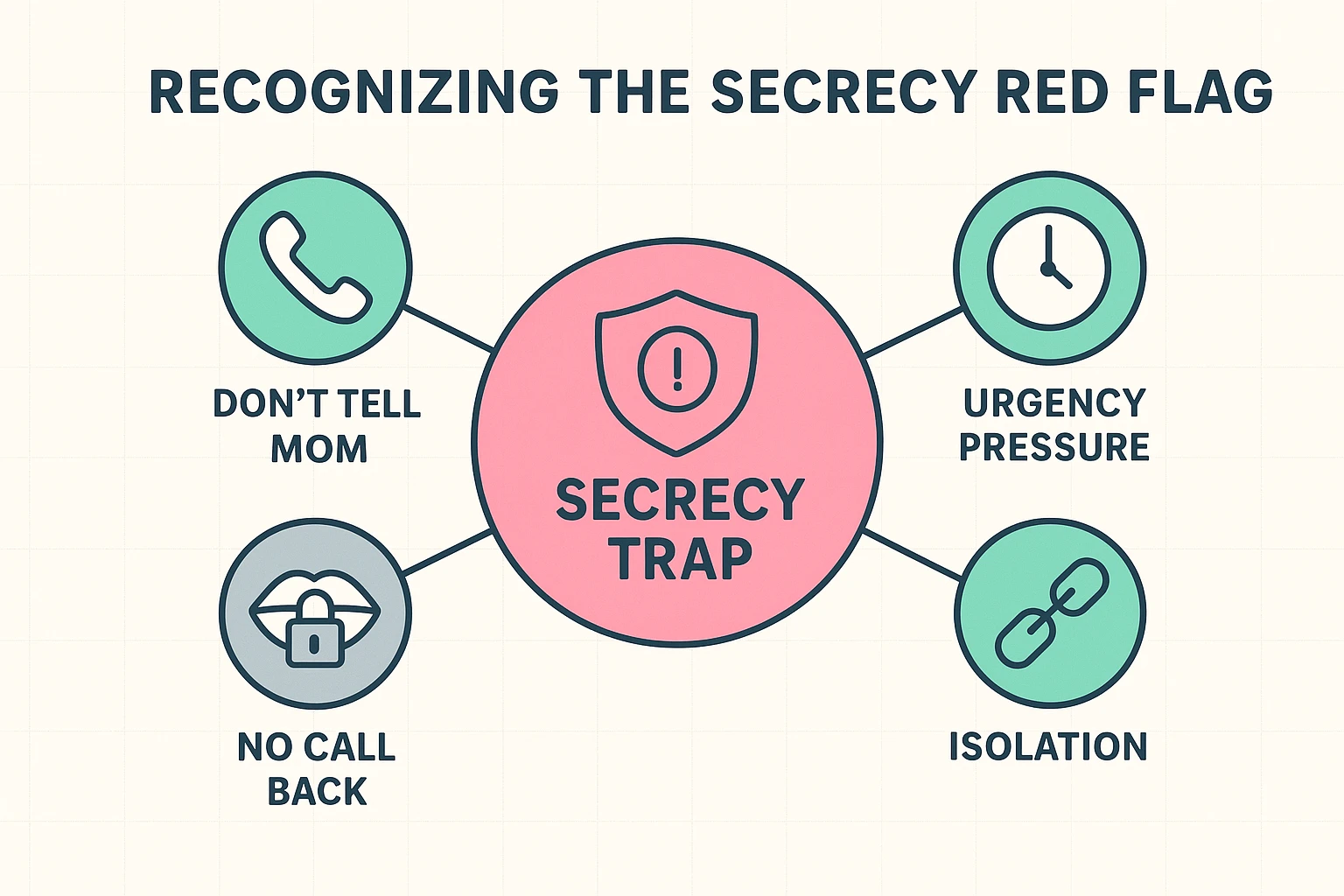
The fake grandchild will inevitably say something like, “Please, whatever you do, don’t tell Mom and Dad. They’ll kill me.” They’ll beg you to keep it between the two of you.
This isn’t just teenage angst. It’s a calculated, engineered barrier to keep you from calling the Family Hub. If a caller ever demands absolute secrecy involving a financial emergency, bells, whistles, and sirens should go off in your head. Secrecy isn’t a plea for help; it’s the absolute, undeniable proof of a scam.
Let’s say you’re still on the phone with the suspected clone. It’s time to play detective. You might have heard advice about setting up a “family safe word.”
That’s a lovely idea, right up until a crisis hits and your heart is pounding, and you suddenly can’t remember if the secret password was “pumpernickel” or “rutabaga.” Instead of a password, use “Shared Sensory Memories.”
These are highly specific, physical questions that an Artificial Intelligence cannot possibly scrape from the internet. Ask the caller, “What color is the hideous rug in my front hallway?” or “Who threw up on the turkey at Thanksgiving 2018?”
An AI doesn’t know about Uncle Larry’s historic gastric distress. If the person on the other end of the line fumbles, tries to stall, or suddenly gets angry at you for asking questions, you have your answer. Hang up the phone.
Often, to make the scam more believable, the “grandchild” will hand the phone to a very serious-sounding “police officer” or “lawyer.” They will give you a badge number, a case file, and try to sound as intimidating as possible.
Never trust the information they provide you over the phone. If they claim to be from a specific local precinct or hospital, hang up immediately.
Look up the actual police department or facility on your own, and check their website for the correct, public non-emergency phone number. Call that official number and ask for the officer they named. You are the boss of your phone, not them.
You don’t have to be a tech wizard to defeat AI; you just have to be prepared. Take five minutes tonight to reach out to your family and establish a protocol.
Tell your kids and grandkids, “If you are ever in an actual emergency, I will always hang up and call you back. If you don’t answer, I will be calling your mother.”
Remind them that you love them, but if they ever need bail money, you fully expect them to remember the name of your childhood dog. By setting these ground rules when everything is calm, you strip the scammers of their only real weapon: your panic.
Yes. It is alarming, but current AI technology requires as little as three seconds of clear audio to create a convincing replica of someone’s voice. This is why you can no longer rely on your ears alone to verify a caller’s identity.
Scammers use a remarkably simple trick called “spoofing.” They can type any number they want into a computer program, and that is the number that will display on your screen. Never trust Caller ID during an emergency request.
Not at all! A family password is a great tool. However, in moments of extreme stress, our memory often fails us. Combining a safe word with “Shared Sensory Memories” (questions only real family members would know) gives you a much stronger safety net.
It’s tempting to give them a piece of your mind, but the safest action is to ask your un-clonable question, realize it’s a scam, and simply hang up. Engaging further can sometimes signal to scammers that your number is active, leading to more junk calls down the road.